Being an ecommerce business owner, your biggest concern is protecting your online store from hundreds of ecommerce security attacks daily. Though WordPress tries to ensure top-notch security for the users, according to a statistics, near about 70,000 WordPress websites, on average, are getting hacked everyday.
Does it mean you should avoid WordPress? NO! Instead, you must always be aware of these attacks and prepare your website against the ecommerce security attacks so that nothing can break down your security system. As you know, precaution is better than cure. So, securing your WordPress site is safer than waiting for an attack proactively.
The Basics of Ecommerce Security
Ecommerce security relates to preventing unwanted access to a business website and all online transactions which take place there. So that you may earn money online without any problems, you need a strong security foundation to establish yourself as a trustworthy and secure online retailer.
Regarding safeguarding your site from potential ecommerce security threats, there is no one-size-fits-all method, regardless of whether you’re constructing a site on an eCommerce platform or a CMS. You can adhere to various industry rules, guidelines, and fixes to reduce security threats.
The six elements of ecommerce security that must be taken into account are as follows:
- Integrity: Verify that an unauthorized party has changed no information. It all comes down to giving reliable, accurate, and consistent information.
- Non-repudiation: It is proof that the information given by buyers and sellers was received. In other words, buyers cannot contest the veracity of a transaction that has been recorded.
- Authenticity: To guarantee the transaction’s security, vendors and buyers must show proof of their identities.
- Confidentiality: Only those with the appropriate authorization can access, modify, or utilize sensitive data.
- Privacy: Protecting client information from unauthorized parties is referred to as privacy.
- Availability: A customer-accessible eCommerce site must be available around-the-clock.
Common Ecommerce Security Threats
1. Financial Fraud
Online fraudsters are becoming increasingly inventive these days, even though obtaining bank account details is typically recognized as the primary hazard underlying eCommerce fraud. These are some financial fraud tactics that online firms could run into.
2. Payment fraud

Credit card information, email addresses, user accounts, and IP addresses are frequently stolen and used by fraudsters to pose as real consumers. This payment fraud may result in bogus accounts, fraudulent purchases, and traffic manipulation.
3. Clean Fraud
This kind of fraud operates by luring cardholders into making purchases on a bogus website or by listening in on the communication between users of the transaction. The inputted personal information will, after that, be accessible to fraudsters. Sometimes, credit card information is purchased on the dark web.
4. Affiliate scams
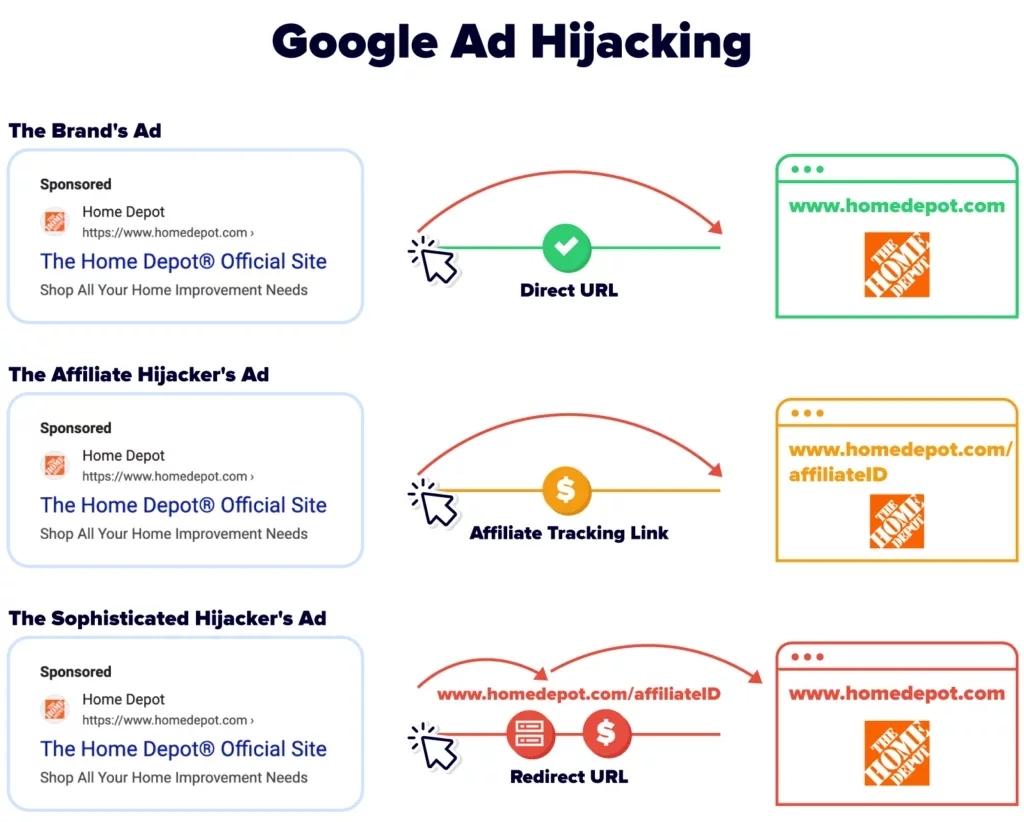
Source: Authority Hacker
To make money, several companies engage in or manage affiliate marketing schemes. Cybercriminals thus use these schemes to generate fraudulent sign-ups and traffic to defraud companies into paying them affiliate commissions.
5. Fraudulent triangulation
The term alludes to the three-step process of attracting customers, gathering their personal information, and using them as props in a nefarious plot which goes against ecommerce security. Fraudsters construct fake websites that advertise cheap, nonexistent goods. As a result, as soon as clients submit their data, it automatically ends up in the wrong hands.
6. Malware
A program or code called malware (malicious software) is intended to damage a server, network, or computer. It often spreads through email attachments or links to rogue websites.
The virus is activated and begins carrying out its purpose, such as stealing sensitive data, getting backdoor access, or monitoring the user’s online activities, as soon as the user clicks on the link or opens the file. Malware can cause great harm to ecommerce security, both financially and reputationally.
The WannaCry virus epidemic cost the UK’s National Health Service some $113 million in 2017 and affected hundreds of thousands of machines across more than 150 nations.
Malware is divided into various categories, including:
- Unwanted adverts – that could damage the user’s device are known as “adware” (software sponsored by advertisements). Due to its high RAM usage, malware might impact your device’s overall performance.
- Trojan horse – a Trojan horse may have been downloaded into the system if there is strange behavior, such as sudden changes to computer settings. Usually, it appears as a free download or an email attachment.
- Fileless malware – infects a computer using trusted applications. It is difficult to detect and get rid of because it does not rely on files and leaves no traces.
- Ransomware – restricts users’ access to their computer systems or private files. They must accede to the demands and pay the ransom to recover access.
- Rootkits – can monitor and access a victim’s computer while evading detection by antivirus software or other eCommerce security programs.
7. Bots
A bot is computer software designed to complete tasks faster and more effectively than a human could. However, hackers can infiltrate a company’s computers and servers by creating bots that mimic human behavior for the monetary benefit and nefarious intent.
Additionally, bots can take advantage of vulnerable identity and access management (IAM) systems, a digital framework that authenticates users and manages their access. Typically, a weak IAM cannot tell the difference between a malicious bot and a real human.
8. Social Engineering Attacks
Most social engineering scams rely heavily on the victim and fraudster developing a personal relationship. Over 30% of successful data breaches, it is said, are the consequence of such attacks. This poses a serious threat to ecommerce security.
These assaults try to gain sensitive information by exploiting human emotions and actions rather than technological flaws. Once the target user has gained the attacker’s trust, manipulation is simple. Social engineering assaults can be recognized in several ways, including suspicious attachments, subpar message layouts or syntax, and uninteresting email subject lines.
9. Phishing
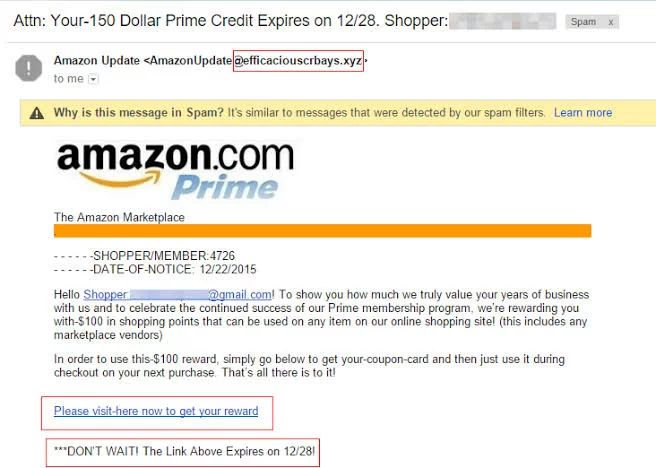
Source: Threatcop
The main purpose of a phishing attack is to steal the victims’ login information. Attackers who use phishing typically duplicate a legitimate web server or application and disseminate dangerous attachments.
Additionally, phone calls, texts, and emails may be used to contact the victims. Scammers may use the submitted credentials for anything if they trick the victim into visiting phishing sites. In some recent phishing scams, the attacker pretended to be an employee of an eCommerce platform and informed the victims that their accounts had been hijacked or that payment irregularities had been discovered.
10. Quid Pro Quo
Scammers pose as resources or help providers for the targeted person to access their device or introduce malware. For instance, the con artist contacts random people and pretends to be a technical assistance specialist solving a problem.
If the user falls for the con, the con artist may demand that they take particular actions, such as downloading ransomware or disclosing personal information, from the victim.
11. Pretexting
Pretexting schemes frequently start with the attacker saying they need the target’s sensitive information. They give carefully designed lies while posing as bank employees, police officers, or coworkers to get the victim to divulge personal information or finish a task.
12. Spam
Spam typically entails sending emails to many recipients, frequently using the “you must take action” email strategy. Businesses lose $20.5 billion annually due to spam due to lost productivity and technological expenditures. Spammers can drop infected links that might lead to compromised databases in the comment section and contact forms on your website. It can harm both your website’s security and your online store’s legitimacy. Additionally, hosting spam comments on your website might result in Google penalizing you. The site’s SEO rating may suffer, and consumers may even stop interacting with your content.
Also Read: Top 11 Anti-Spam Plugins for Better Browsing Experience
13. DoS and DDoS Attacks
DoS (Denial of Service) and DDoS (Distributed Denial of Service) attacks aim to take down a website as their primary objective. Attackers repeatedly send queries to the website from unidentified IP addresses. The number of connections used is one of the main characteristics that separate DoS from DDoS attacks. The latter uses many internet connections to interfere with a network or server, whereas the former uses one connection.
As a result, it is more challenging to identify the origin of DDoS assaults because they come from many areas. Entrepreneurs should pay extra attention to ecommerce security during busy times like Black Friday and Cyber Monday. For a US-based business, a DDoS assault might cost up to $218,000 dollars.
14. Brute Force Tactics
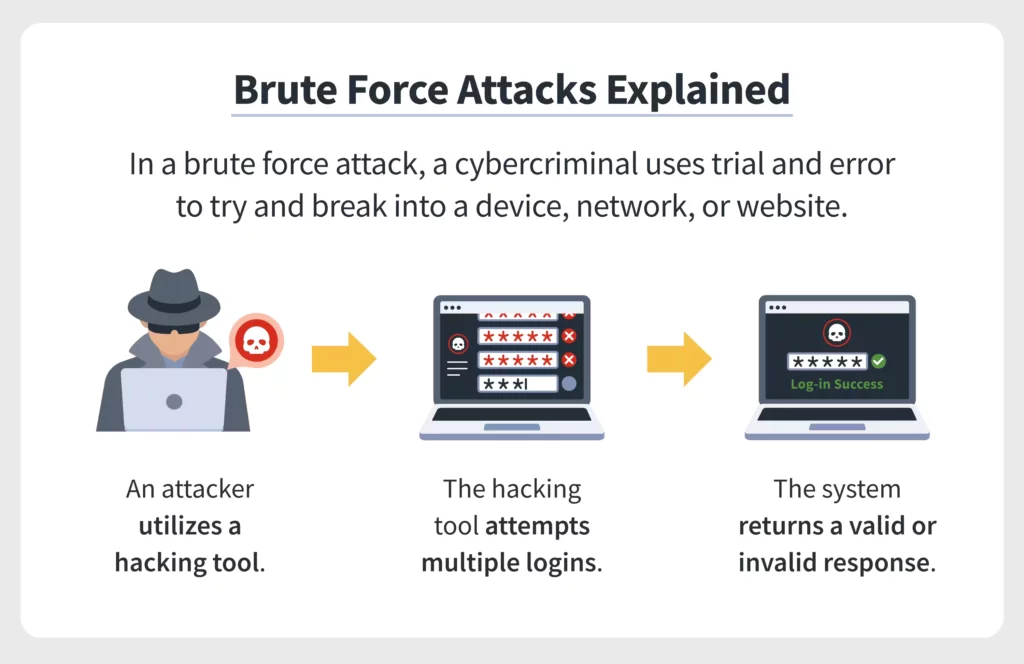
Source: Norton
Brute force strategies function by merely guessing the login information needed to access the admin panel of your e-commerce website. In order to find the right password, hackers utilize sophisticated software to test various combinations of letters, numbers, and symbols.
Hackers can access your important website database once they have successfully brute-forced their way into your website. Sensitive information, such as your customers’ identities, bank account information, and other private data, may be stolen or sold for profit.
The data of 21 million individuals were hacked in a large brute force attack that targeted the Alibaba-owned eCommerce site Taobao in 2016. The hackers used a database of 99 million usernames and passwords to access the accounts.
15. E-Skimming
E-skimming, often known as a Magecart attack, is a hacking method that uses undetectable malicious code. The code steals their transaction data as clients make purchases on a hacked website. Additionally, hackers carry out nefarious operations using the data they have stolen.
The dark web is used to sell the financial information of online shoppers, including full names, card verification codes, and expiration dates. 2019 saw a significant e-skimming attack that targeted Macy’s, a well-known American department retailer. Both the homepage and the checkout page had a Magecart script installed by the attackers.
Proved Ecommerce Security Tips to Protect Your Online Store
Ecommerce Security should not be taken lightly. The trust in digital security has been severely eroded by significant data leaks. Customers feel at ease making payments through well-known platforms like PayPal, Stripe, etc. But it takes a little more persuasion to trust you with their credit card information, isn’t that right?
Therefore, you must first make sure that there is nothing that can compromise data on your site in order to persuade them to buy from your store. On this reason, we’ll go over some expert advice for eCommerce security that can make it impossible for hackers to access your site.
Create secure passwords for your ecommerce security
The majority of software still uses passwords as the default access method, despite competition from technologies like facial recognition and multi-factor authentication (MFA).
Since we require passwords to access each service or website we visit, many users find it simpler to use the same password for several different services.
The issue with this ecommerce security strategy is that reused usernames and passwords can be used to log into numerous services, resulting in widespread fraud once hackers have obtained them.
Make long, distinctive passwords by combining symbols, lowercase and uppercase characters, and numbers. The complexity of the password also rises.
- A password should never be used for multiple services.
- Update passwords every few months or when one was unintentionally shared with someone else.
- Keep private information, such as your birth date, social security number, or home address, to yourself.
- Create a reCAPTCHA to increase the security of logins.
- Restrict login attempts to stop an attacker from figuring out the user’s password.
- One efficient defense against brute-force assaults is to lock off accounts after numerous unsuccessful login attempts.
- Additionally, think about utilizing a professional password manager, such as the one provided by NordPass, to manage login information. It can also be used to create solid and one-of-a-kind passwords. Your passwords are also kept in an encrypted format, making them impossible for hackers or malicious malware to access.
Select a Secure Host
A hosting company is in charge of keeping the files for your website. Therefore, it’s crucial to pick a trustworthy service that offers safe and dependable data storage for your eCommerce site.
When selecting a hosting company, consider features like SSL certificates, DDoS protection, encryption techniques, and malware detection. Make sure it also provides backups so you can easily restore the functioning of your website in the event of a ecommerce security compromise.
Among the services included in web hosting plans are a free SSL certificate and a 99.9% uptime guarantee. Spend some time considering which plan will best meet the requirements of your eCommerce website.
Get an SSL Certificate

To comply with PCI regulations, all eCommerce enterprises must implement the SSL (Secure Sockets Layer) protocol. Make careful to choose the SSL certificate that best suits the needs of your website and business from the range of options available.
A properly implemented SSL protects both your website and the data of users. All data entered into your online business is encrypted, making it more challenging for hackers to access and understand the information.
Once an SSL certificate is installed, the website’s URL will switch from HTTP to HTTPS. Since a conventional HTTP protocol does not encrypt connections in the same manner that HTTPS websites do, the “S” stands for ecommerce security.
Customers will feel more confident shopping at your online store because many browsers will display a padlock icon in the address bar. This digital certificate will increase site security and its SEO because Google prefers websites that use the HTTPS online protocol.
Install security plugin
Along with installing SSL, ecommerce websites must also include multi-layer security technologies like plugins and antivirus software. Security plugin can do several things to improve eCommerce security, like finding bots, restricting unreliable networks, and getting rid of malware. The following are some of the most well-liked security plugins if you develop an online store using an ecommerce website builder or a CMS like WordPress. Some of the most famous ones are listed below:
- Wordfence
It is the most widely used WordPress security plugin, with more than four million downloads. Wordfence detects and prevents harmful requests with dubious code or content using an integrated malware scanner. Additionally, it can restrict login sessions to defend your website against brute force attacks.
- Keyy
Keyy compels customers to utilize its mobile app to access WordPress rather than typing in a username and password. Additionally, you may use your fingerprint or a 4-digit pin as two-factor authentication to further secure the iOS and Android-compatible software.
- Sucuri
One of this lightweight plugin’s primary functions is activity auditing. It gives website owners the option to monitor any modifications that are made. Additionally, it has a capability that allows users to identify malware remotely and strengthens ecommerce security.
5. Install anti-malware software
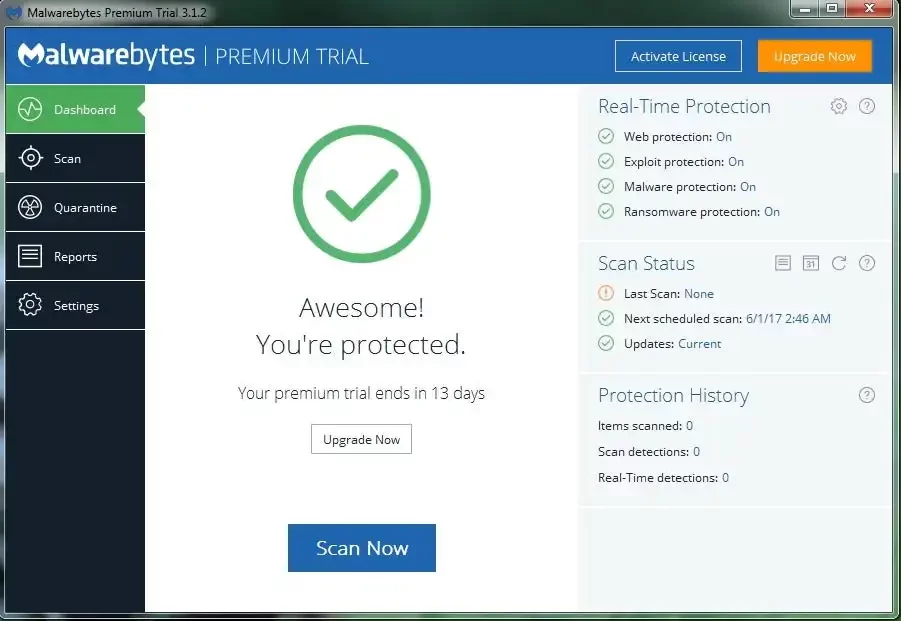
Anti-malware software Malware assaults have advanced in sophistication with ecommerce security measures. Therefore, spending money on appropriate safety for your company is crucial. Several well-known anti-malware programs that work with Windows, Macs, and Linux include the following:
- Endpoint Security by ESET
ESET, well-known for its strong, portable cybersecurity solutions, aids in defending companies of all sizes against the most cutting-edge cyberattacks. Small company owners or anyone opening an online store can test it out for free for 30 days before committing to a plan.
- AVG AV software
It defends your website in a variety of ways, including by providing remote admin tools to control website security while on the go and instantly alerting users to threats and ecommerce security. AVG offers a 30-day money-back guarantee even if their internet antivirus subscription doesn’t come with a free trial.
- Norton
A password manager is included in each of its plans, and a complete refund will be given if a virus can’t be eliminated from a user’s device. To detect and thwart various online dangers, Norton integrates device security, online privacy, and identity protection. A free trial lasts for seven days and offers full ecommerce security.
6. Plan frequent site updates
Web developers release new ecommerce security updates to address flaws and introduce new remedies. To stop hackers from exploiting those holes, your ecommerce site’s essential software must be updated. Additionally, make sure to regularly review and update the plugins and themes on your website. The updates typically include fixes that fix known problems or offer new features.
By enabling automatic updates, you can keep your website current and safeguard ecommerce security. In addition to saving you a ton of time on your website maintenance schedule, this will stop your website’s essential software from running out of date.
7. Make regular backups
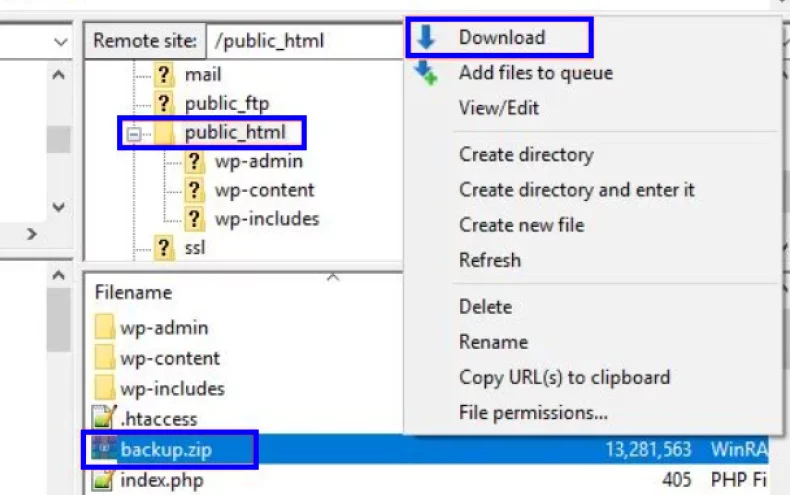
Regular website backups might help shield your site from hazards like faulty databases or ecommerce security flaws. When planning your website backups, take into account how frequently you alter your website’s content and appearance.
Even though most hosting companies offer automatic backups, it is a good idea to frequently download copies of the files and database on your website. Site backups shield you from losing important data or having to start from scratch in the event of an unplanned event.
8. Include two-factor authentication (MFA)
In order to use this approach, users must provide a one-time passcode (OTP), respond to a security question, or authenticate using their fingerprints.
Microsoft claims that MFA can thwart over 99% of potential online threats. So implementing MFA is an excellent way to improve eCommerce security. Installing Google Authenticator and a security plugin like Wordfence Login Security on your mobile device will enable MFA.
9. Use a CDN (Content Delivery Network)
A CDN is a collection of dispersed servers that routes user requests to the ones that are nearby. It is a fantastic ecommerce security solution for a global ecommerce company. Furthermore, ecommerce websites frequently handle requests from many different regions and experience tremendous traffic. The site can lose visitors if it takes too long to load.
Therefore, a trustworthy CDN provider like Cloudflare can prevent unanticipated spikes in web traffic and server breakdowns by effectively spreading your site’s content and providing a quicker response. Additionally, employing a CDN will speed up page loading time with features like picture scaling since you’ll probably host many media files. Nestify, a CDN provider, offers Cloudfare CDN for complete protection of your site.
10. Control user permissions and roles

Regardless of the kind of website you operate, user role management is essential for security reasons. It is a crucial ecommerce security audit practice to avoid unintentional site configuration. You may limit who can perform operations like installing updates, themes, and plugins or altering the PHP code by controlling user roles and permissions. You can also install custom login plugins for giving limited access to your subscribers/users.
WordPress, for instance, enables site administrators to give other users access to six predefined roles. The positions are super admin, editor, author, contributor, and administrator. In addition, each role is limited to a particular set of tasks (known as capabilities).
Be sure to bear the following advice in mind before allowing anyone accesses to your website:
- Give users only the access they require: Preventing users from making unauthorized changes or deleting data without permission is an essential ecommerce security measure.
- Do not have too many site administrators: Examine a person’s job responsibilities and their level of competency carefully before allowing them admin access. Alternatively, grant them access at a lower level.
- User permissions and roles can be customized: To personalize the responsibilities assigned to each user, use a free plugin like User Role Editor. The plugin is useful when you need extra hands to manage your website or block users from accessing it.
11. Utilize protected payment gateways
Credit card transactions are authorized by a payment gateway, which also collects settlement and pays the funds into your account. In other words, the entire eCommerce transaction process is automated. PayPal, Google Pay, and Apple Pay are some popular payment gateways.
A secure payment gateway offers you top-notch ecommerce security measures since it must adhere to the strictest PCI standards. This is known as PCI DSS compliance. Verify the security steps your preferred payment gateway uses to safeguard transactions, such as:
- Data encryption: A payment gateway encrypts a customer’s credit card information using a public key. The data is then decrypted using a different (private) key. The payment gateway employs the private key and an algorithm that ensures that no unauthorized party may access this information.
- Many providers need Security Sockets Layer (SSL) certificates since they encrypt the communication between the client’s browser and the server.
- Secure transmission of a customer’s credit card information during an online transaction is ensured by Secure Electronic Transaction (SET). SET stops retailers and hackers from accessing private data by hiding card details. Digital signatures are also necessary for further authentication and confidentiality.
- Tokenization: substitutes random characters for a credit card number. The tracking of the token requires a decryption key. Hackers won’t be able to decipher the token if there is a breach.
12. Do Not Store Confidential Information
Sensitive data shouldn’t be stored in a website’s database, which breaches PCI requirements and leaves it open to a hacker attack. Leave the payment processors in charge of handling all consumer data.
If necessary, keep any sensitive information on offline storage devices like USB drives, DVDs, or external hard drives to keep it safe from hackers. Remember to keep it in a secure location where only you have access.
13. Improve Staff Training
The laws and regulations governing the protection of user information should be known to your team. They shouldn’t exchange login information, and you should look over employees with access to private customer data.
To prevent your employee from committing a cybercrime against your company after they submit their resignation, delete all their information and cancel all their access.
14. Watch Out for Negative Behavior
Keep an eye out for any odd activity if you want to avoid any hostile attacks from slipping through the cracks of ecommerce security. This could prevent a fraudulent transaction from occurring, saving you a lot of headaches and money.
You can make use of specialized monitoring software that keeps tabs on the action in real-time and alerts you to any dubious transactions. For instance, a con artist utilizes several cards to place orders or orders when the cardholder isn’t using the card.
15. Inform Your Customers
Some ecommerce security lapses occur at your client’s end rather than your own, and they can employ weak passwords or give critical information to hackers via phishing websites. By educating your clients, you can address these e-commerce security issues.
Inform them of the dangers posed by improper security procedures. You can instruct them to use secure passwords and explain the principles of phishing.
Conclusion
Building an ecommerce website and starting an online business may be interesting and fun challenges. After all, the market is expanding, and if you play your cards well, early retirement could be in your future.
However, many new business owners need to pay attention to the ecommerce security of their e-store websites. The most crucial aspect of an ecommerce website, or at least it should be, is security. Online business owners without adequate protection expose their clients, their brand, and themselves to fraud and identity theft. Not to mention that stolen credit card information might ruin your finances, causing severe losses for your company.
Fortunately, you can follow many simple ecommerce security strategies to protect your website. You don’t need to be a computer genius to use them. Additionally, it will be difficult to retain existing clients after a breach, let alone attract new ones. Therefore, the main goal of ecommerce security is to ensure that both your company and your customers feel secure.
FAQs
What Are the Main Risks of an eCommerce Site That Isn’t Secure Enough?
There is a greater chance of cyberattacks when ecommerce security measures are lax. If your eCommerce site is hacked, you will lose your reputation, see a decline in search engine rankings, and deal with refund requests and legal action from clients whose data was compromised.
How Should I Respond If My Website Was Hacked?
To lessen the harm caused by malware, we’ve created a list of procedures to fix a hacked website. As an alternative, think about having a ecommerce security specialist retrieve it. If you lack confidence in your technical abilities, the latter is advised.
How much does maintaining ecommerce security on a WordPress site cost?
There are numerous free WordPress ecommerce security plugins that are sufficient to safeguard your e-commerce website. Once the company is up and operating, you can upgrade to a premium version that fits your spending plan.