Recent years have witnessed a tremendous rise in cyber security risks on a global scale. As companies transitioned to remote work settings, cybercriminals took advantage of misaligned networks. 2021 gave a hike in the number of cyberattacks worldwide by 125%. More so, the volume of cyberattacks continued to increase in 2022, posing a threat to businesses and individuals.
In 2022, the United Kingdom had the highest rate of cybercrime victims per million internet users, with 4,783 victims per million internet users – an increase of 40% from the data for 2020. In 2022, the United States had the second-highest rate of victims per million internet users, with 1,494, a decline of 13% from 2020.
Brute force attacks are a type of hacking that rely on trial and error to decipher sensitive information like passwords and login credentials. It’s a foolproof method for breaking into people’s accounts and corporate networks. The hacker will try a large number of possible combinations of usernames and passwords before finally gaining access.
Types of Brute Force Attacks

- Standard Brute Force Attack
In a basic brute force attack, the hacker guesses the user’s password without any aid from automation. This is done with the help of standard password combinations or PIN codes.
Many people, even in today’s world, use insecure passwords like “password123” or “1234”, or engage in poor password etiquette like reusing passwords across several websites, making such attacks easy to execute. Hackers who perform just minimal reconnaissance work can often guess a user’s password based on information such as the user’s favorite sports team’s name.
Dictionary Brute Force Attack
An attacker using a dictionary attack would pick a target and try each possible password with that person’s username. The attack is not a brute force attack in and of itself, but it can be a useful tool in the hands of a malicious user.
Dictionary attacks get their name because criminals modify words in dictionaries using random symbols and digits. The success rate of such an attack could be higher, and it takes a lot of time to set up, especially when compared to more modern methods.
Hybrid Brute Force Attack
When a hacker employs a dictionary attack and a standard brute-force attack, they launch a hybrid brute-force attack. The hacker must first know the username for the target account before attempting a dictionary attack or other simple brute-force methods.
The attacker generates a list of possible words, then tries various combinations of letters, numbers, and special characters to crack the password. Passwords like “Delhi123” “HarryPotter123” are easy for hackers to crack because they combine recognizable words with arbitrary digits and letters.
Reverse Brute Force Attack
A known password, typically obtained via a network breach, is the starting point for a reverse brute force attack. They put that password to use by scouring databases of millions of user names for a match. A database of usernames could be scanned for a match using a commonly used weak password, such as “Password123.”
Credential Stuffing
Credential stuffing exploits users’ lackadaisical approach to password security. Attackers compile lists of username/password combinations and try them on other websites to compromise even more user accounts. If people frequently use the same password for different online accounts and social media profiles, this strategy can succeed.
What is the Purpose Behind Brute Force Attacks?

- Exploit Ads or Activity Data to Profit From
In order to make money through advertising commissions, hackers could launch a brute force attack on one website or network of websites. Some tactics include distributing malicious advertisements on widely visited websites to profit from its clicks and views, Hackers could also redirect visitors from a legit website to unauthorized ad sites which are paid to display advertisements. Installing tracking malware the website and/or its visitors to extract information to be sold to advertisers is also one of the factors,
- Steal Private Information
Access to a user’s private account can yield sensitive information ranging from banking records to medical history. When an attacker gains access to the user accounts, they can steal their identity, money, or use that information to launch additional attacks.
Businesses face the risk of having its most sensitive data compromised if hackers gain access to their systems and steal customer information or login credentials.
- Distribute Malware
The hackers’ motivations to wreak havoc and display their nefarious abilities go beyond financial gains. Malware may be sent via email or SMS, hidden on a fake website, or legit website visitors could be redirected to malicious sites. When the attacker infects a user’s machine by use of malware, it spreads out across to carry out even more extensive cyberattacks.
- Hijack systems for malicious activities
When a malicious actor uses a network of compromised computers to launch a wide attack, the network is called a botnet. This is often in form of DDoS attack, in which several computers work together to overwhelm a system’s defenses.
- Inflict damage on the credibility of a business or online portal
In an effort to steal information, hackers may resort to brute force, which can extremely damage an organization’s reputation besides its financial stability. Attacks that infect websites with obscene or offensive text and images can also damage their reputation and increase the likelihood that the sites will be shut down.
How to Avoid Brute Force Attacks?
1. Enhance Your Methods of Password Security

Passwords should be as difficult to crack as possible to protect against brute force attacks that specifically target them. Users can play a significant role in securing their and their organization’s data by adopting more robust passwords and adhering to established password best practices. Attackers will have a more complex and longer time trying to guess their passwords and may give up as a result. Best practices for more secure passwords include:
- Generating lengthy, complex passwords: Passwords should be longer than 10 characters and contain a combination of upper- and lowercase letters, symbols, and numbers. This way, the time and effort required to crack a password go from a few hours to several years, unless the hacker has access to a supercomputer. Longer passwords are safer, but some sites have limits on how long a password can be, so it’s best to use complex passphrases instead. Use difficult passphrases to thwart attacks that rely solely on a dictionary. Passphrases consist of a series of words or characters meant to be difficult to guess.
- Specify guidelines for developing secure passwords: If you truncate words in your password, it will make the password look random to anyone else. To do this, one can either eliminate vowels or use only the first two letters of each word, and then piece together a meaningful phrase from the remaining words. One common practice is to abbreviate commonly used words.
- Don’t use predictable passwords: Passwords like “password,” “12345,” or “password” are the most common and, therefore, the most vulnerable. Hackers use strategies to break into user accounts based on commonly used words or phrases in passwords.
- Always use different passwords for every online service: Hackers use a technique called “credential stuffing” to see if previously used passwords are still being used across different websites. Unfortunately, this is effective because people frequently reuse passwords for various online accounts.
- Implement the usage of a password manager: This tool allows the generation of strong, different passwords for each online service that requires one. It can generate and store user login information for various websites, allowing users to access multiple accounts with a single login to the password manager. If you use password manager, you can make strong passwords without worrying about forgetting them, losing them, or having them stolen.
2. Password Security Should Be Improved
User adherence to recommended best practices for creating and using passwords is largely irrelevant if their organization cannot adequately prevent data breaches caused by brute force attacks. Organizations also bear some of the responsibility for user security and network hardening through measures like:
- Passwords can be difficult to crack by encrypting them with a high rate, such as 256 bits. This reduces the likelihood of a brute force attack succeeding.
- System administrators can increase the security of password hashes by employing a cryptographic technique known as salting the hash. To make a password more secure, they add a salt—a series of random letters and numbers kept in a different database—to it.
- Authenticate users with more than just a password by enabling multi-factor authentication (MFA). Using multi-factor authentication (MFA), a user will be asked for additional verification of their identity after entering their password. This could be a code delivered via SMS, displayed on their device, or even a fingerprint scan. When this is in place, it becomes much more difficult for the attacker to break into a user’s account or a company’s system, even if they have the user’s login information.
- The success rate of brute force attacks can be lowered by limiting the number of times a user can re-enter their password credentials. Locking an account completely after multiple failed login attempts prevent the hacker from repeatedly testing username and password combinations, and preventing additional login attempts after two/ three failed logins can deter a potential attacker.
- Using a CAPTCHA box during the login process can stop an attacker from using a computer to try to brute force their way into a user account or business network. Typing text images that appear on screen, checking multiple image boxes, and identifying objects are all possible CAPTCHA choices.
- Create a blacklist of IP addresses to prevent access to certain websites: Protecting a company’s network and its users from known attackers is facilitated by deploying a blacklist of IPs used in attacks. To thwart future attacks, it is crucial to maintain an accurate blacklist.
- Log out of inactive accounts: Inactive accounts give hackers a way into your network and should be immediately closed. To prevent accounts from being used in a brute force attack, businesses should regularly delete inactive ones or delete them as soon as employees leave the company. Employees with elevated permission levels or access to confidential company data should consider this especially.
3. Maintain Password Safety and Support

Businesses need to do more than raise employees’ consciousness about the importance of good IT security and implement stringent measures to prevent data breaches.
- Provide password education: Users need to know what adequate security and password usage best practices look like and how to spot the signs of cyberattacks. In addition, they require consistent training and informational updates to stay abreast of emerging risks and instill best practices. Corporate password manager tools, also known as vaults, allow users to store complex passwords and eliminate the risk of password loss, which could compromise sensitive company information.
- Keep an eye on live networks: Multiple failed login attempts and logins from unfamiliar devices or locations are tell-tale signs of a brute force attack. Businesses must keep their networks and systems under constant surveillance for any signs of unusual or malicious activity and immediately shut them down.
4. Passive Backend Protections for Passwords
- High encryption rates: Passwords should be encrypted with the highest encryption rate possible, such as 256-bit encryption, to make it more difficult for brute force attacks to succeed on the system. The more bits there are in the encryption system, the more secure the password will be.
- Salt the hash: Adding a random string of letters and numbers (called salt) to the password itself is another way for administrators to increase the randomness of password hashes. The password should be hashed after this string is added, which is why it needs to be stored in a separate database. By adding salt to the hash, even if two users share the same password, their resulting hashes will differ.
- Two-factor authentication: Two-factor authentication (2FA) and an intrusion detection system capable of identifying brute-force attacks are both options open to system administrators. This necessitates a second, independent verification step, such as the use of a physical USB key or fingerprint biometrics scan, after a successful initial login.
- Limit the number of login re-tries: Reducing the possibility of being the victim of a brute-force attack is facilitated by limiting the number of login attempts. For instance, if a user has three chances to enter their password correctly before being locked out for several minutes, the delay can be substantial. It may encourage the hacker to move on to an easier target.
- Account lockdown after excessive login attempts: Locking accounts after too many failed login attempts are useless because a hacker can always try again later. This behavior can be discouraged by locking the account and requiring the user to contact IT to unlock it. However, while shorter lockout periods may be more convenient for users, they can be more easily exploited. If there are too many failed logins after the short lockdown, you can switch to the long-term one as a countermeasure.
- Throttle rate of repeated logins: In order to slow down an attacker’s efforts, you can increase the time between each login attempt. After a failed login attempt, a timer can prevent another one until some predetermined amount of time has passed. Your real-time monitoring staff will have some lag time before they can detect this threat and begin working to mitigate it. If hackers see no point in trying, they may give up and go elsewhere.
- Required Captcha after repeated login attempts: After several failed login attempts, a Captcha will be required to prevent automated programs from gaining access to your system via brute force. There are many kinds of captchas; some need you to retype the text from an image, while others have you select a box or pick out an object. It can be used before the first login and after each failed attempt, regardless of the method you choose.
- Education on online privacy: User behavior is the most critical factor in password security, so it is crucial that users be taught how to create secure passwords. Password management can be made easier by informing users about best practices and available resources. Kaspersky Password Manager is one service that allows users to securely store their complex, difficult-to-remember passwords instead of keeping them in plain text on post-it notes around the house. Users often prioritize convenience over safety, so it’s essential to equip them with simple safeguards.
- Watch out for accounts in real-time for strange activity: Login activity can be monitored to detect any suspicious behavior, such as multiple failed login attempts or using a different device to access the account. Seek out unusual behavior patterns and take immediate action to prevent attacks. Keep an eye out for blocked IP addresses, locked accounts, and user contact to verify the integrity of account activity (if it looks suspicious).
5. Employ Pen Testing Methods
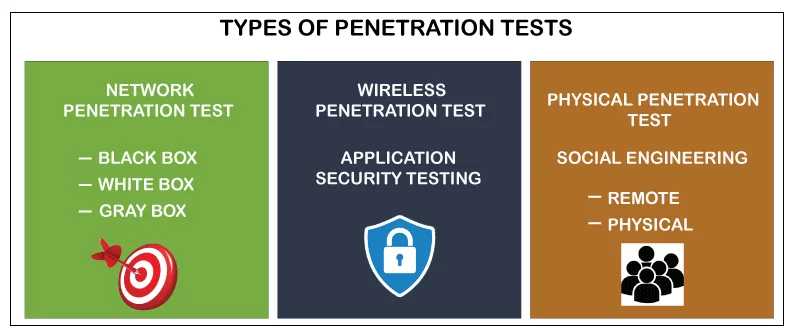
Source: Javatpoint
Many organizations employ penetration testing to secure their infrastructure and information from brute force attacks. To know more about these methods, read the blog.
Also Read: Cyber Threats Unveiled: A Deep Dive into the Shadows of Cybersecurity
Conclusion
Attackers’ overly forceful attempts to breach security have given rise to the term “brute force.” Although brute force attacks have been around for a while in the cyber world, they continue to be a popular strategy for cybercriminals.
Also Read: How Brute Force Attacks Are Done On WordPress and How to Protect Your WordPress Site
FAQs
Q: What is a brute force attack?
A: brute force attack is a cyber attack where an attacker repeatedly tries different combinations of username/password until the correct one is discovered, which gives them access to a system, website, or application.
Q: How does a brute force attack work?
A: The attacker uses a software program that quickly generates and tests millions of combination for usernames and passwords.
Q: What is the purpose of a brute force attack?
A: Brute force attack aims to gain unauthorized access into a system, website, or application. Once the attacker has uncovered the right username and password , they can use this information to log in and potentially access sensitive information, modify data, or even damage the system.
Q: How can a brute force attack be prevented?
A: There are several stepsto prevent a brute force attack, including:
- Use strong and unique passwords for your account.
- Enable two-factor authentication on your accounts.
- Use a password manager to generate and store strong, unique passwords.
- Limit the number of log-in attempts in order to prevent attackers from guessing your password repeatedly.
- Regularly monitor the logs for signs of a brute force attack.
Q: What are the signs of a brute force attack?
Signs of a brute force attack can include:
- Several failed login attempts in a short period of time.
- Unusual traffic/ activity on your website or server.
- Suspicious IP addresses which repeatedly attempts to log in to your system.
- Unresponsive or slow website or server.
Q: What are the most common targets in brute force attacks?
A: Brute force attacks may be targeted at a system that requires a password for access, which includes websites, email accounts, bank accounts, and even computer systems.